Cybersecurity web design that turns risk-aware buyers into qualified leads.
Most cybersecurity companies lead with technical language and lose the board members and budget holders who think in financial risk, not threat vectors. We build websites for cybersecurity companies that communicate business risk clearly, establish certification credibility immediately, and convert the right searches into contract conversations.
Trusted by over 100+
businesses around the world.
From penetration testing firms and managed SOC providers to incident response specialists, MSSP operations, Cyber Essentials assessors, and compliance-focused security consultancies, we help cybersecurity companies communicate their expertise to non-technical buyers, rank for the searches that drive contracts, and convert cautious prospects into engaged clients.
































Decision makers are evaluating your capabilities and signing with a competitor.
Most cybersecurity companies have genuine technical depth, real certifications, and a track record of protecting clients from significant threats. The problem is that the buyers who control the budget are not CISOs. They are CFOs, operations directors, and board members who think in terms of financial exposure and reputational risk. When the website leads with threat vectors and security architecture, those buyers close the tab before they understand why the company matters to them.
Cybersecurity buyers are cautious, compliance-driven, and acutely aware of what is at stake. They are choosing a company to trust with their most sensitive systems. When the website cannot demonstrate specific competence through verifiable credentials and real-world evidence, that contract goes to a competitor whose site made the decision feel safer.
01
Every buyer type lands on the same generic page.
An SME owner, an enterprise CISO, and a regulated financial institution have completely different concerns. A single homepage that tries to address all three convinces none of them to take the next step.
02
The messaging speaks to security engineers, not to budget holders.
Technical language loses the CFO and the board before they form a business case. If the risk cannot be understood in thirty seconds in financial terms, the evaluation ends before it begins.
03
The company is invisible for the searches that drive contracts.
Decision makers searching for penetration testing, managed SOC services, or GDPR compliance support are not finding the site. Those are contracts going to better-optimised competitors every week.
04
Certifications and accreditations are not visible where they count.
ISO 27001, CREST membership, SOC 2, and Cyber Essentials Plus are what a cautious buyer checks before anything else. When they are buried, the trust required to proceed never forms.
05
There is no evidence of real-world capability.
No anonymised case studies, no incident response narratives, no quantified risk reduction outcomes. A buyer who needs to justify the spend to their board has nothing to build a business case with.
Qualified contract leads, faster procurement cycles, and a company that stands apart from every generic MSSP.
When the website translates technical expertise into business risk language and serves each buyer with precision, the quality of every inbound lead changes. Decision makers arrive already understanding the risk. The contract conversation starts with fit, not with education.
01
Board-level buyers understand the risk before the first meeting.
Business-focused risk language, financial exposure framing, and clear service outcomes mean a CFO or operations director arrives for the initial conversation already convinced there is a problem worth solving and a budget worth allocating.
02
The company ranks for every service search that drives pipeline.
Penetration testing, managed SOC, incident response retainer, GDPR compliance support. Each of those searches represents a buyer in an active procurement cycle. The site captures that traffic before a competitor does.
03
Certifications build trust before any technical conversation takes place.
ISO 27001, CREST, Cyber Essentials Plus, and SOC 2 displayed prominently give a cautious buyer the compliance confirmation they need to move from research to engagement. The procurement barrier drops before the first call.
04
Case studies prove capability in the language buyers understand.
Anonymised breach scenarios, penetration testing outcomes, and quantified risk reduction evidence give procurement teams and board risk committees exactly what they need to justify the contract internally. The sales cycle shortens.
05
Each buyer type follows a journey built around their specific concerns.
SME owners, enterprise CISOs, regulated financial institutions, and board-level risk committees each find messaging, proof points, and service pathways tailored to their situation. The conversion rate across every segment improves.
06
Thought leadership keeps the company visible for a longer buying cycle.
Compliance deadline guides, threat landscape updates, and regulatory explainers keep the company front of mind with buyers who are months away from making a decision. When the moment arrives, the brand is already trusted.
Start your project.
Your business deserves a website that’s not just visually impressive, but also built to deliver real results. Whether you’re launching a new site or enhancing an existing one, Typza is ready to help. Schedule a call today and let’s craft a digital presence that truly works for your brand.


Why cybersecurity buyers choose their provider based on the website before a conversation is booked.
Cybersecurity procurement is one of the most risk-averse buying processes in any sector. Buyers are evaluating not just capability but trustworthiness, compliance, and the consequence of getting the decision wrong. The company whose website communicates specific expertise, verifiable credentials, and real-world evidence most clearly to the right buyer wins the evaluation. The one that does not is filtered out before the shortlist is formed.
A technically flawed or poorly performing website is uniquely damaging for a cybersecurity company. It is not just a missed opportunity. It is the most powerful negative signal a prospective client can receive about the company's actual standards. The website has to perform at the level the company is promising to protect.
The cybersecurity companies building the strongest enterprise pipelines are not always the most technically sophisticated. They are the ones whose websites speak plainly to every buyer type, prove capability through credible evidence, and make the procurement decision feel safe and straightforward. A website built to that standard changes every contract conversation from the first search result.

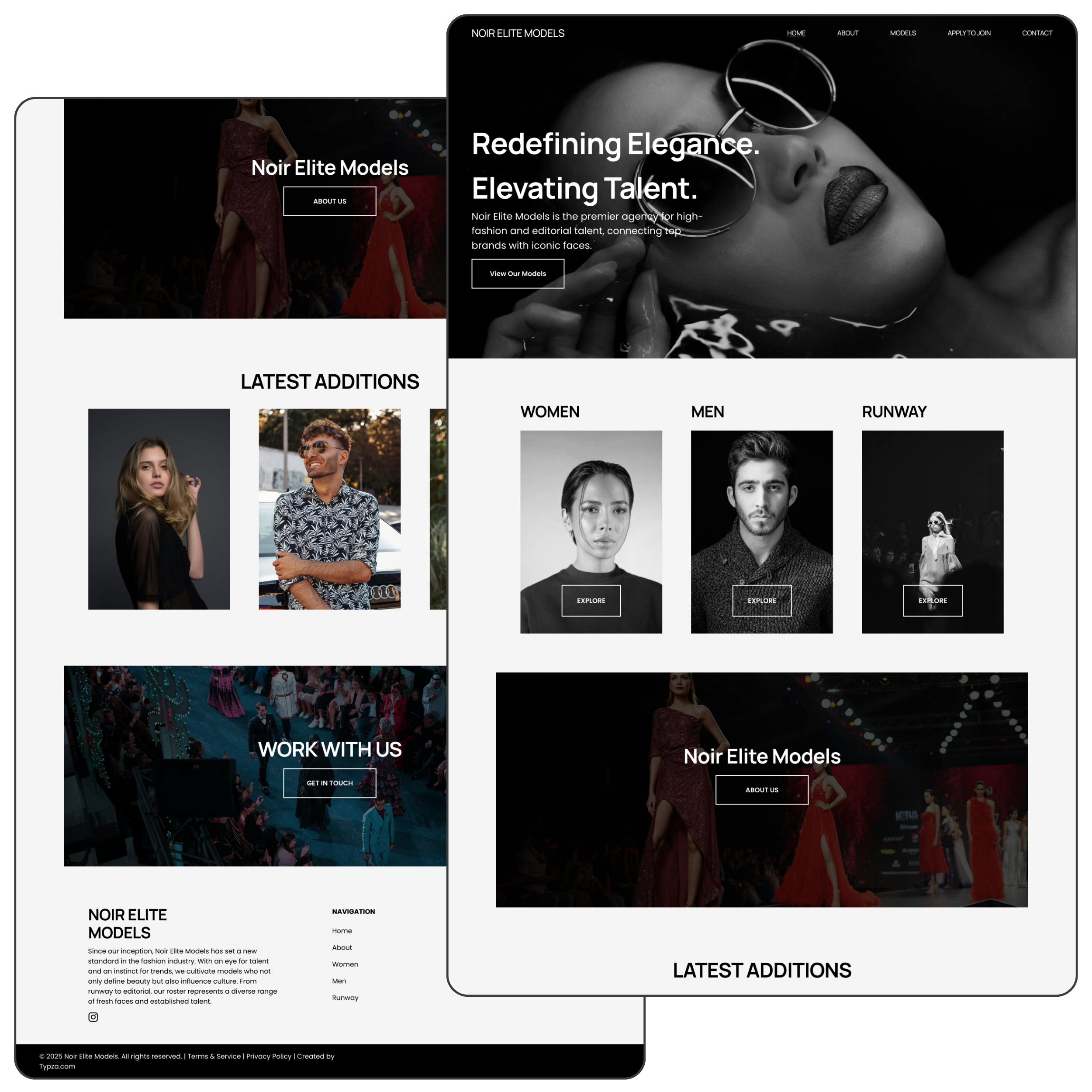
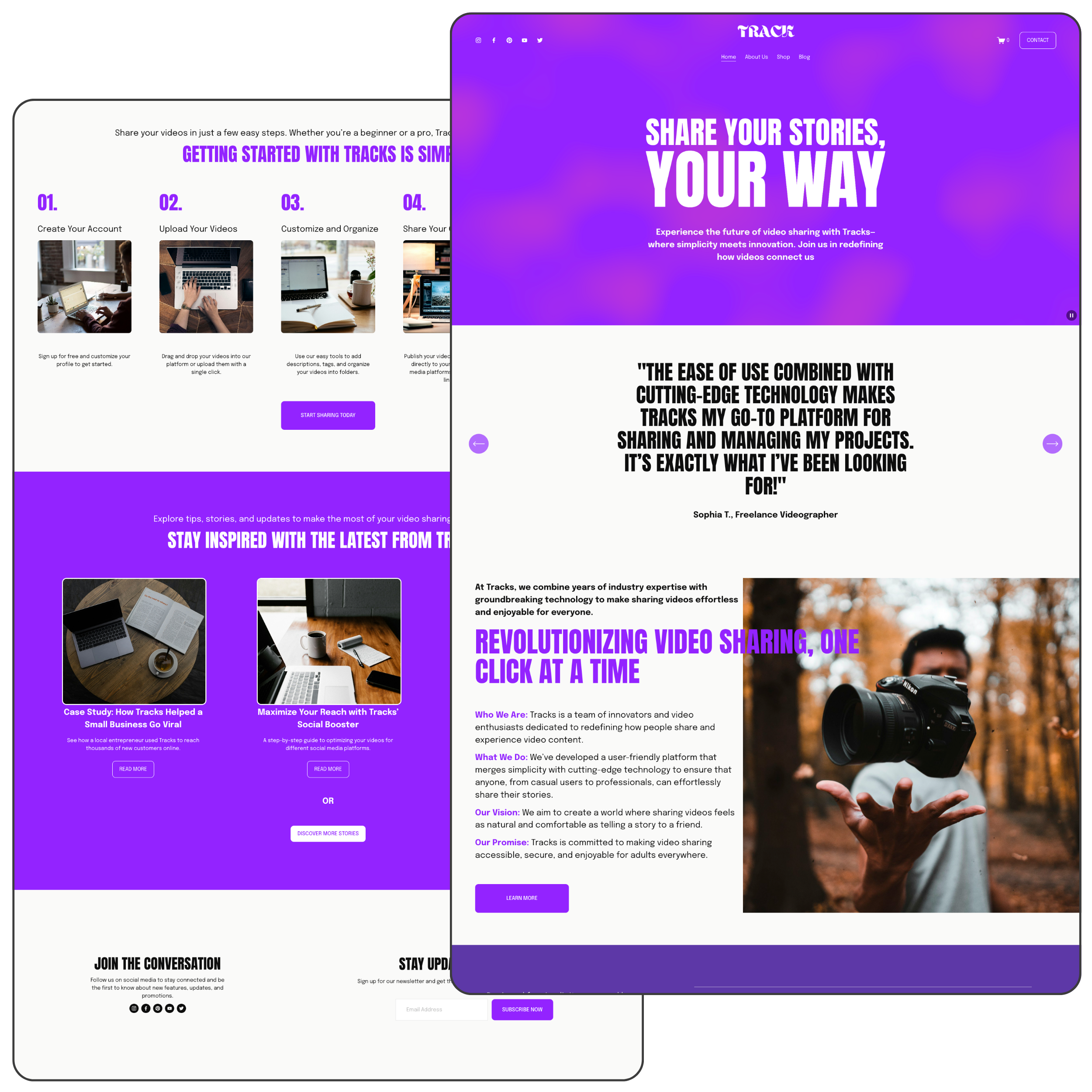
Websites built to win security contracts, not just impress security teams.
Every project is built to ensure the right decision maker finds the company, understands the risk, and takes the next step with confidence.
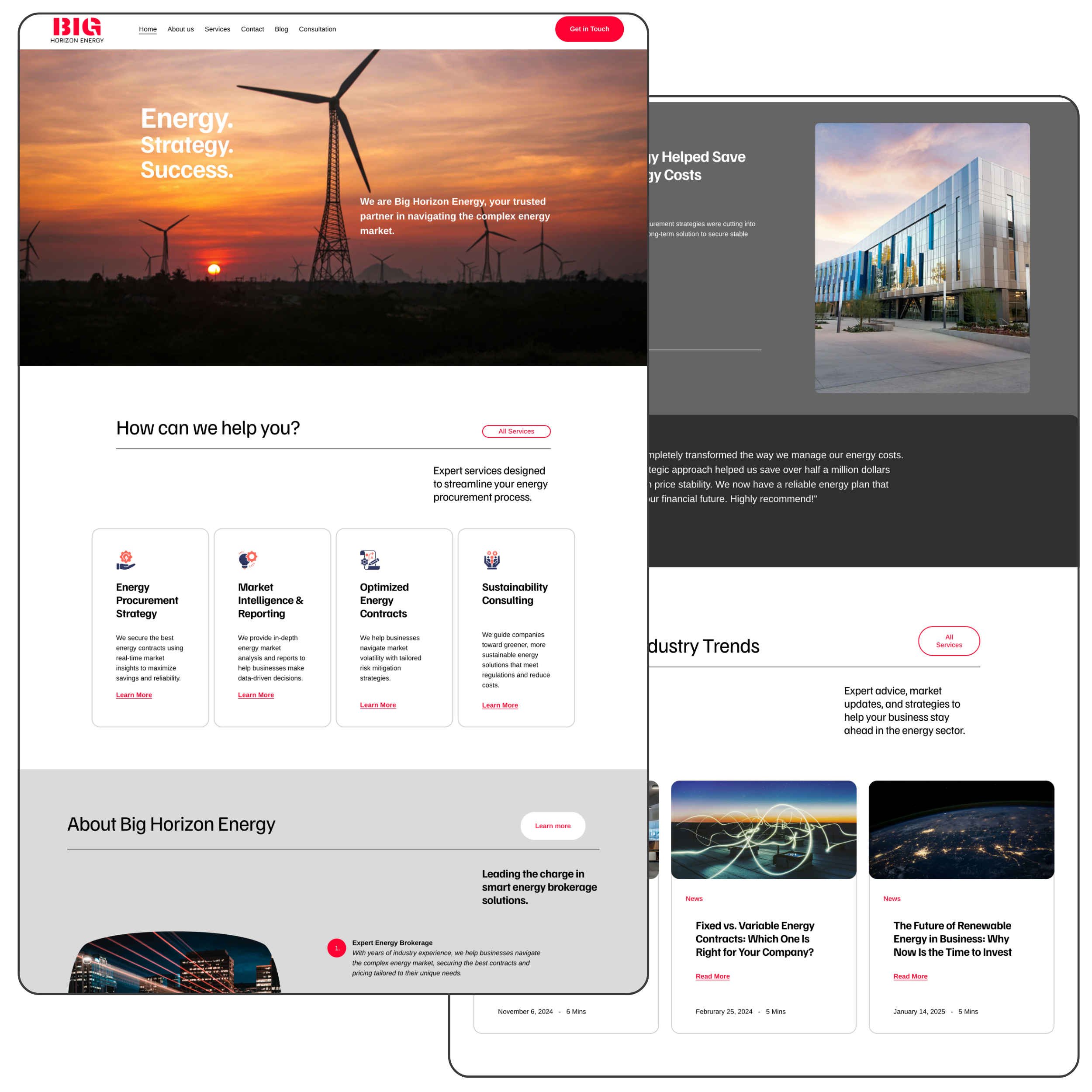
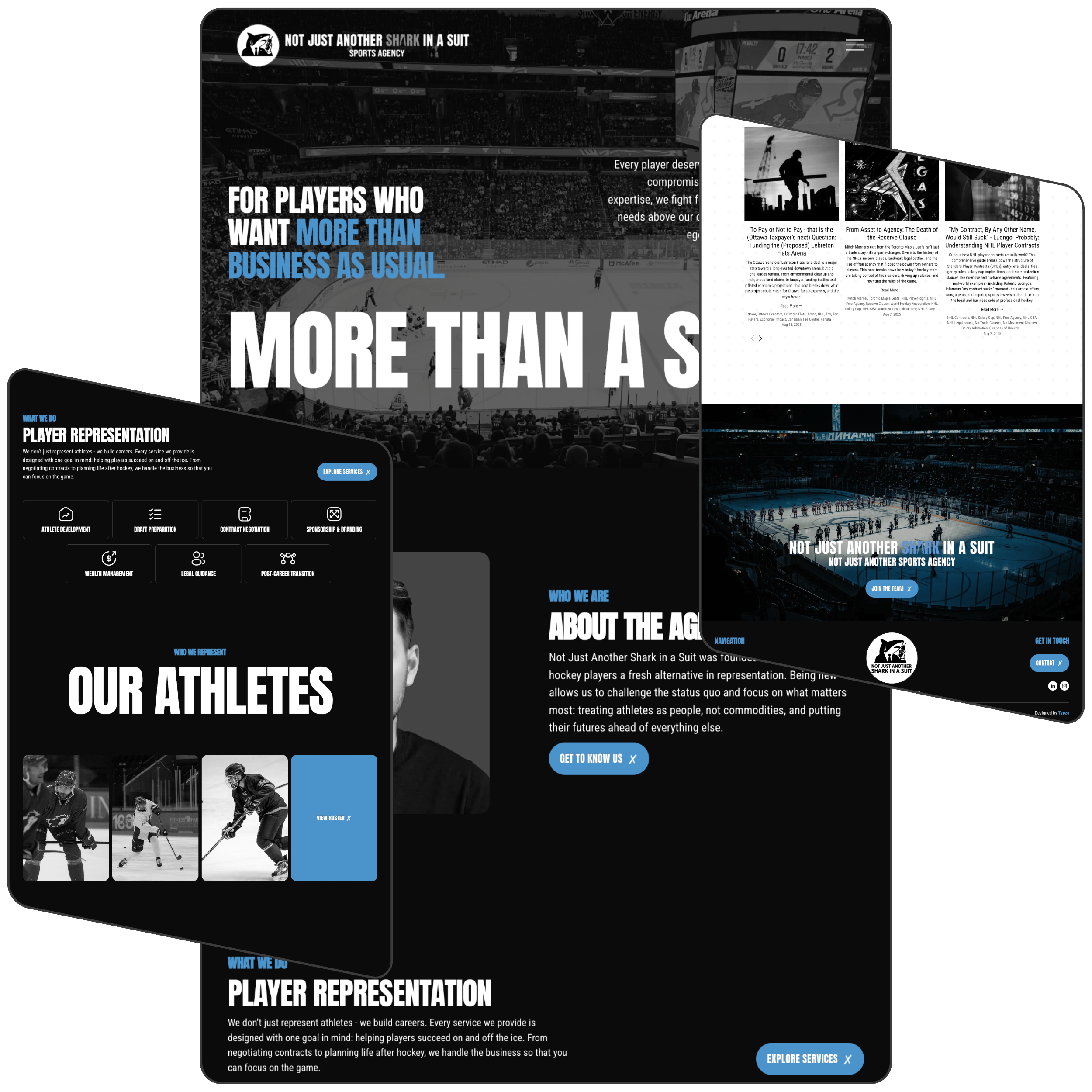
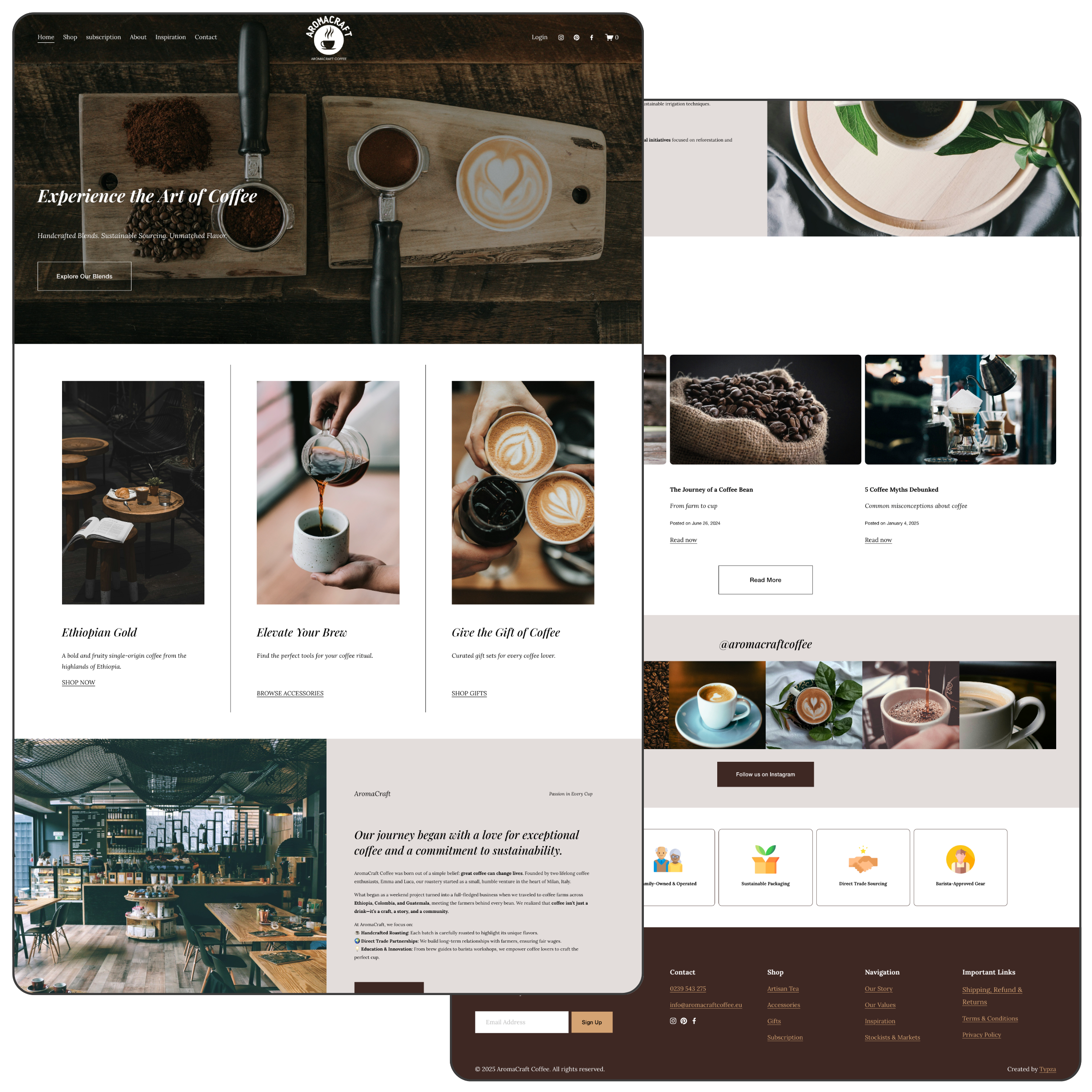
Real results for real businesses.
Every project is built with one focus — helping cybersecurity companies attract better-qualified leads, communicate their expertise to non-technical buyers, and convert high-intent searches into contract pipeline.
A website that makes your expertise legible to the buyers who control the budget.
A generalist agency does not understand how board-level cybersecurity buying decisions are made, what certification architecture builds procurement confidence, or how to build service pages that rank for the compliance and threat-specific searches that drive the highest-value contracts. They build cybersecurity websites. We build contract pipelines for security companies.
Every decision on the page is made around what a risk-averse, compliance-driven, non-technical buyer needs to see before they are ready to engage. The result is a website that translates technical depth into business language, establishes credibility from the first visit, and converts cautious researchers into qualified contract leads.
Custom web design services for cybersecurity companies.
Designed to attract clients and communicate security expertise.

Update your own cybersecurity website easily.
Once the site is live, the team can publish threat intelligence content, update certifications, and add new case studies without waiting for a developer or paying for every change.
Empower your team with full control and flexibility.
-
The site belongs to the company from day one, with full access and no ongoing dependency on us unless the team chooses it.
-
Give marketing leads, compliance managers, or content teams the ability to update the site without accessing anything outside their role.
-
Add new service pages, publish threat intelligence articles, and edit copy visually exactly as it will appear live, with no code required.
-
Capture enterprise contract enquiries, penetration test requests, incident response retainer applications, and SME protection leads with forms tailored to each buyer type.
-
Add new service pages, buyer segment journeys, compliance framework pages, and threat-specific content as the company's capabilities and target markets evolve.
-
Share client security reports, penetration test summaries, or compliance documentation securely without making them publicly visible.
-
Every page reflects the company's visual identity and technical authority consistently, so the credibility of the brand never wavers across any section of the site.
-
Publish compliance deadline guides, threat landscape updates, and regulatory explainers that build long-term search authority and keep the company visible to buyers throughout a longer procurement cycle.
-
Share security assessment frameworks, compliance checklists, and service scope documents directly from the site so buyers can build their internal business case without waiting for a sales call.
-
See which service and compliance pages drive the most qualified traffic, where contract leads originate, and what content is shortening the procurement cycle most effectively.
-
A fixed price agreed upfront with no surprises and no hidden costs as the site and service portfolio grows.
-
Help is available whenever the team needs it, whether that is publishing a threat advisory before a major vulnerability disclosure or updating certifications after a renewal audit.
-
Lead data and sensitive commercial information submitted through the site is protected on infrastructure built to the highest security standard, with SSL included as standard.
Start your project.
Your business deserves a website that’s not just visually impressive, but also built to deliver real results. Whether you’re launching a new site or enhancing an existing one, Typza is ready to help. Schedule a call today and let’s craft a digital presence that truly works for your brand.